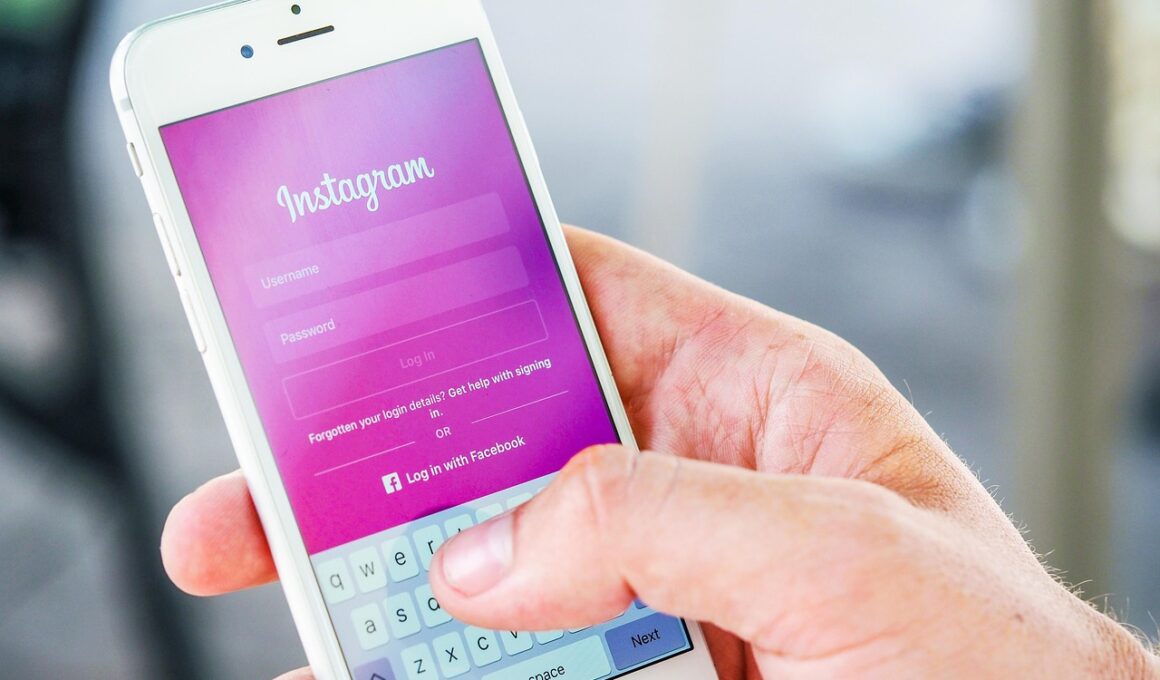
Recognizing Fake Login Pages on Social Platforms
With the rise of online interactions, recognizing phishing attempts has become crucial. Phishing is a deceptive method where attackers create fake login pages to steal personal information. Often, these malicious pages imitate legitimate social media platforms. To safeguard your sensitive details, it’s vital to understand how to identify these fraudulent sites. A common tactic is to check the URL carefully. For instance, authentic platforms usually have URLs that look like www.secureplatform.com. If the URL contains misspellings or unusual characters, it’s likely a scam. Another significant indicator is the absence of HTTPS in the URL; secure sites use this protocol to protect users. Furthermore, examine the design and layout of the page. Fake login pages often have grammatical errors, unusual logos, or poorly designed interfaces. Additionally, trust your instincts. If something feels off about a login request, take precautions. Avoid entering your credentials and report suspicious activity immediately. Lastly, ensure your devices have security software updated; this plays a crucial role in detecting phishing threats. Staying vigilant can help protect not just your account but also your personal information.
Common Characteristics of Phishing Pages
Recognizing characteristics of phishing pages can save you from falling victim. Fake login pages often resemble genuine sites, but they have distinct features that can signal danger. Firstly, look for discrepancies in design elements. Legitimate sites maintain a consistent brand image, including specific colors and fonts. Secondly, phishing sites may ask for excessive information that a legitimate platform wouldn’t request. Authentic login forms typically only require a username and password. If a site asks for additional data, like credit card numbers or social security details, it is a warning sign. Furthermore, phishing attacks often use urgency to create panic—claims that your account will be suspended unless you act immediately. If you feel pressured into providing information, stop and reassess the validity of the request. Check the footer of the page for contact information; legitimate companies provide clear avenues for customer support. In phishing contexts, this information may be missing or incorrect. Lastly, always be cautious of unsolicited emails or messages that direct you to login pages. Verify these communications directly with the platform.
Another essential practice is ensuring your browser has updated security features activated. Modern browsers often include tools designed to flag suspicious websites. Before entering any sensitive information, check for security warnings. If a site is flagged, do not proceed. Additionally, consider using password managers, which provide an extra layer of security. These tools not only help generate strong passwords but also ensure that you only input passwords on trusted platforms. Always installation of two-factor authentication (2FA) for your social media accounts enhances account security. This method forces potential attackers to access a second device to log in. When you enable this, even if someone gets your password, they can’t access your account without your mobile device or email. Also, stay informed about new phishing techniques; awareness is one of the best defenses. Regularly visiting security blogs or forums can provide real-time insights into emerging threats. Encouraging conversations about online security within your network will keep everyone on high alert. Building a culture of caution around technology can protect not just individuals but entire communities as well.
Importance of Reporting Phishing Attempts
Reporting phishing attempts assists not only yourself but also the larger online community. Once you recognize a fake login page, take action by reporting it to the appropriate authorities. Most social media platforms have dedicated tools for reporting suspicious activities. Utilizing these tools helps the platform take swift action against malicious users. Additionally, document your findings when reporting. Include screenshots of the fake page, the URL, and any suspicious communication that led to the phishing attempt. This detailed information can help investigators respond effectively. Moreover, informing your friends and family about the scam can prevent others from falling victim. Sharing your knowledge regarding phishing sites creates awareness among your circle, potentially saving their accounts from compromise. Furthermore, educational campaigns by social platforms and cybersecurity firms often rely on user reports to adapt their strategies against phishing. Through this collective effort, we can fortify defenses and diminish the number of successful phishing attempts. Remember, staying informed and proactive makes a significant difference in the fight against online fraud.
An additional protective measure is observing social media behavior closely. Being cautious about unsolicited requests from friends for personal information or financial help is essential. Sometimes, compromised accounts may send messages that seem authentic but are malicious attempts to gain your trust. Always verify such communications directly, preferably through a separate channel. Additionally, limiting the personal details shared on social platforms preserves your security. The less information attackers have, the harder it is for them to craft convincing phishing attempts. Maintain privacy settings updated to restrict who can see your posts and personal data. Furthermore, be wary of friend requests from unknown individuals. Genuine profiles usually consist of activity over time, whereas fake accounts often have minimal history. Regularly review your list of friends and connections; removing suspicious accounts reduces your risk of engagement with phishing tactics. Also, educate yourself on common varieties of phishing, such as spear phishing or whaling, which target specific individuals. Understanding these methods further enhances your ability to recognize and protect against potential scams, equipping you with valuable skills in today’s digital landscape.
Staying Safe on Social Media Platforms
To maximize your safety on social media, integrate a combination of strategies and practices. Initially, always access your social media accounts by typing the URL directly into your browser, rather than clicking links in emails or messages. This habit avoids accidental navigation to malicious sites. Regularly update your passwords, making them strong by mixing letters, numbers, and symbols. Strong passwords are harder to crack and an essential part of your security. Following that, use unique passwords for each account to ensure that if one account gets compromised, the others stay secure. Moreover, be discerning about the information you share publicly. Displaying too many personal details can potentially help attackers craft targeted phishing attempts. Utilize privacy settings to control who views your content and information. If your platform allows for it, enable alerts for unrecognized login attempts; this feature can notify you if someone tries to access your account from an unfamiliar device. Be informed about the most recent security updates from your social platforms; they often release patch updates to protect against known vulnerabilities.
In conclusion, being proactive regarding social media security is vital for your personal safety and data integrity. Recognizing phishing attempts is only part of a broader set of practices that lead to safer online experiences. Monitor your accounts regularly to spot any unauthorized activities. If you notice anything suspicious, take immediate action by changing passwords and notifying your network. Additionally, consider periodic security audits of your accounts, where you can evaluate and update settings to maintain optimal security. Be committed to lifelong learning regarding cybersecurity; it is a continuously evolving challenge. Regular engagement with credible resources will keep you abreast of new threats and effective defenses. Joining communities focused on cybersecurity can also offer support and shared knowledge that strengthens your understanding. Overall, fostering an environment of security awareness involves personal vigilance while also encouraging others to be cautious. By sharing knowledge and resources, we contribute to a safer online community for everyone. Finally, remember that safety is an ongoing journey; vigilance and education today lay the groundwork for your secure online experience tomorrow.